Resolv's USR Hack Shows Why 'Fully Backed' Stablecoins Still Break
Resolv's pitch was simple: USR was supposed to be a crypto-backed stablecoin with a delta-neutral design, a separate risk-absorbing layer, and a collateral pool meant to keep the dollar peg credible.
Then on March 22, 2026, an attacker showed the market something more important than the collateral story: if your issuance layer can be broken, your backing story stops mattering almost instantly.
According to Web3 Is Going Just Great's incident summary, the attacker minted and dumped tens of millions of unbacked USR, pushing the stablecoin as low as $0.14 and extracting roughly 11,400 ETH, or about $24 million. Cointelegraph's same-day report said onchain watchers first identified a 50 million USR mint tied to only $100,000 of USDC, followed by another 30 million USR, and estimated roughly $25 million had already been cashed out. Cointelegraph also reported a flash crash to $0.025 in the main Curve pool before a partial rebound.
That spread in numbers is normal during the first hours of a live exploit. What matters is not whether the attacker got $24 million or $25 million. What matters is that the market immediately stopped believing that 1 USR = 1 dollar.
The official line was calm. The market was not.
The Resolv Labs statement linked from the incident page, and shown in the screenshot below, tried to draw a line between the exploit and the protocol's reserves:
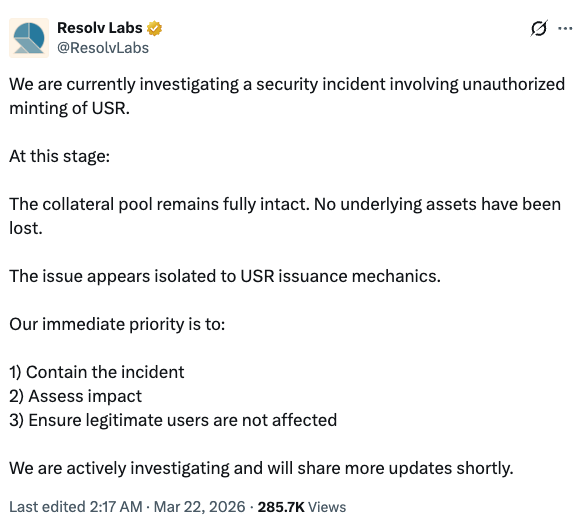
In the original post on X, Resolv wrote that it was "investigating a security incident involving unauthorized minting of USR," that "the collateral pool remains fully intact," and that the issue "appears isolated to USR issuance mechanics" (tweet).
That statement may be technically true. It is also the exact kind of statement that sounds reassuring only if you think stablecoin risk begins and ends with reserve solvency.
It doesn't.
Stablecoins fail in at least three different ways:
- the collateral is not there,
- the collateral is there but cannot be realized when needed,
- or the token supply can be corrupted faster than the system can defend itself.
Resolv appears to have run into the third category, and that is enough on its own to break the product.
Why "collateral remains intact" is not a defense
This is the key point users miss after hacks like this.
Once unbacked supply is minted and sold into the market, the collateral pool is no longer the whole story. Even if the reserves are untouched, you now have:
- more claims outstanding than should exist,
- panic selling from anyone trying to exit first,
- DEX pools taking the first hit,
- and every downstream integration suddenly repricing the token as suspect.
That is exactly what happened here. Web3 Is Going Just Great noted that some DeFi protocols paused USR-exposed strategies to limit downstream damage. That is rational behavior. If a stablecoin's mint integrity is compromised, every protocol using it as collateral, LP inventory, or accounting unit has to assume the problem is bigger than the first tweet admits.
For LPs, that matters immediately. If you were sitting in a USR/USDC or USR/other-stable pool during the exploit, you were not protected by the fact that "underlying assets have not been lost." The market does not wait for a post-mortem. It reprices on contact.
The uncomfortable part of the Resolv design
Resolv's documentation makes the architecture look operationally controlled. Its docs say token supply operations are governed by ExternalRequestsManager contracts, and that addresses interacting with those contracts must be whitelisted (docs). Mint and redemption requests move through a request lifecycle before being completed.
That setup is not proof of what broke, and we should be careful not to overstate root cause before a formal incident report exists.
But it does tell us something important: this was not a simple "the market got emotional" depeg. This was an issuance failure in a system with explicit mint controls. As Cointelegraph reported, D2 Finance speculated that either an oracle was manipulated, an offchain signer was compromised, or validation between request and mint completion failed.
Those are very different failure modes technically. Economically, they all cash out the same way:
someone creates supply they should not have, someone sells it into real liquidity, and everyone else discovers that "fully backed" was only as good as the mint gate.
Update: Chainalysis adds a much more specific failure path
New reporting from Chainalysis gives the market a more concrete explanation for how that mint gate appears to have failed.
According to Chainalysis, the attacker compromised Resolv's AWS KMS environment, gained the ability to use the protocol's privileged SERVICE_ROLE signing key, and then pushed fraudulent mint approvals through the normal requestSwap -> completeSwap flow. In that reconstruction, the contracts did not fail because of a traditional smart contract bug. They failed because they trusted a valid signature more than they enforced an onchain issuance ceiling.
That is an important distinction. Chainalysis says the minting path enforced a minimum output amount, but not a meaningful maximum tied to collateral. No hard collateral-to-mint ratio. No oracle check. No onchain cap that would have stopped a wildly inflated mint even after a key compromise. Once the signer environment was effectively under attacker control, the protocol's own authorization logic could be used to print counterfeit supply at scale.
If that account is accurate, it sharpens the earlier list of possible causes considerably. This now looks less like a generic validation failure and more like a very specific architecture problem:
- a privileged offchain signer sat upstream of issuance,
- the signer could authorize the final mint amount,
- and the contract apparently lacked a hard onchain limit that said "even a valid signature cannot mint this much against that deposit."
That combination is how a roughly $100,000 to $200,000 USDC-funded flow can allegedly become 80 million USR.
Chainalysis also adds a useful detail about the cash-out path. After minting the unbacked USR, the attacker reportedly converted it into wstUSR, the wrapped staked version of the token, before rotating into other stablecoins and ultimately into ETH. That matters because it suggests the attacker was not just dumping the raw counterfeit asset as fast as possible. They were also using Resolv's own wrapper and staking mechanics to route around immediate liquidity constraints while the market was still figuring out what had happened.
In other words, the newer picture is worse, not better. The exploit was not merely "someone minted too much somehow." It appears to have been a full demonstration that offchain key security and onchain issuance limits have to work together. If either one is missing, the reserve story stops being the system's primary defense.
This is not just a hack story. It's a market-structure story.
The most interesting part of this event is not that a stablecoin got exploited. That happens. The interesting part is how quickly a design that looks conservative on paper can become toxic in live trading.
USR was not supposed to behave like a reflexive algorithmic stablecoin. It had collateral, risk segmentation, and structured yield mechanics. Resolv's own materials emphasize that RLP is supposed to absorb residual risk so USR can remain stable. But that framework is designed for market losses and strategy losses. It is not a substitute for issuance integrity.
Once counterfeit supply hits a pool, the first line of defense is not treasury design. It is market depth.
And market depth is usually thinner than protocols pretend.
That is why these incidents turn ugly so fast:
- the attacker sells faster than governance can react,
- LPs absorb toxic flow first,
- aggregators keep routing until guards flip,
- and the peg chart becomes the real post-mortem before the written one arrives.
Cointelegraph's reporting that the main Curve pool briefly traded down to $0.025 is a perfect example. Even if the token later recovers part of the move, the damage is already done. Some users sold the bottom. Some LPs got loaded with broken inventory. Some protocols had to pause and eat the operational cost.
Those losses are real even if the protocol later says the reserves were untouched.
What users should watch next
As of March 22, 2026, the incident story still looks live rather than settled. So the right questions are not philosophical. They are operational.
Watch for:
- a real post-mortem that names the failure mode, not just a reassurance thread,
- whether redemptions resume cleanly and at what terms,
- whether Curve and other USR pools recover depth or stay structurally impaired,
- whether any integrators permanently remove or haircut USR exposure,
- and whether Resolv socializes losses, reimburses users, or tries to ring-fence blame around secondary-market holders.
That last point matters more than teams admit. When a stablecoin exploit creates bad supply and dumps it onto DEX liquidity, the protocol can say "the collateral pool is intact" all it wants. The economic question is who ends up wearing the mismatch.
Usually, it is some combination of:
- whoever bought the counterfeit supply,
- whoever LP'd against it,
- and whoever was slowest to hit the exit.
The takeaway
The cleanest lesson from the USR exploit is also the simplest:
Stablecoin safety is not just about assets. It is about control over issuance.
Resolv may still prove that the reserve side of its system was untouched. If so, fine. But the market already delivered the harsher verdict: a stablecoin whose minting path can be abused is not safe in the way users think the word "backed" implies.
That is the real damage here.
Not just the estimated $24 million to $25 million extracted by the attacker.
Not just the depeg.
But the reminder that in DeFi, "fully collateralized" often gets marketed as if it means "structurally robust." It doesn't. If the issuance rail breaks, the peg breaks with it.
For traders, that means stablecoin risk belongs in the same bucket as bridge risk and oracle risk: boring until the exact moment it is catastrophic.
For LPs, the takeaway is harsher. If you are warehousing a stablecoin in a pool, you are not just underwriting reserve quality. You are underwriting mint logic, signer hygiene, integration controls, and emergency response speed too.
That is a lot of hidden surface area for something called "stable."